Loading...
Hopefully not for too long :)
Hopefully not for too long :)
Infrastructure as code tool to spin up and automate infrastructure, safely and effeciently
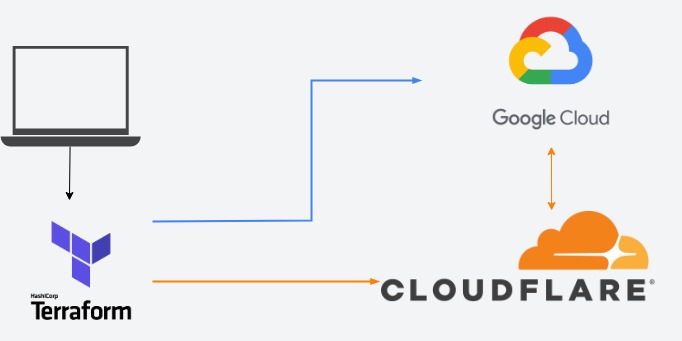
Terraform is a famous open-source infrastructure-as-code tool that enables users to define and provision infrastructure resources through code across multi cloud providers. I have utilized it for automating the provisioning of Google Cloud Platform resources. In particular, I employed it for setting up virtual machine instances, as well as firewall rules, IP addresses, and Cloud Storage buckets for storing states and artifacts from Cloud Build. Moreover, I integrated Terraform with Cloudflare to automatically create DNS records that point to newly provisioned VM instances external IPs and my domain registry, abdulsamisahil.net.
terraform {
backend "gcs" {
bucket = "my-portfolio-387110-tfstate"
prefix = "/tfstate/my-portfolio"
}
required_providers {
google = {
source = "hashicorp/google"
version = "~> 4.65.2"
}
cloudflare = {
source = "cloudflare/cloudflare"
version = "~> 3.0"
}
}
}I have utilized terraform backend remote feature which enables me to store the state files remotely in a gcs, allowing for secure and collaborative infrastructure management. The google provider facilitates the creation, modification, and removal of resources within my GCP project, while the Cloudflare provider manages changes to DNS records in my Cloudflare account. Together, these providers enable me to automatically provision and manage infrastructure resources in GCP while also managing DNS records in Cloudflare.
provider "cloudflare" {
api_token = var.cloudflare_api_token
}
provider "google" {
credentials = file("terraform-secrets.json")
project = var.project
region = var.region
zone = var.zone
}I securely managed access to the Cloudflare API key and Google resources by creating a role-specific service account in Google Cloud Platform with only the necessary predefined roles to handle VMs, networks, buckets, and artifacts created within the project. Additionally, to restrict access exclusively to DNS records, I assigned the Cloudflare API key with the least privileges required to manage DNS records. To authenticate Terraform to access these services, I furnished the JSON key of the service account to Terraform and retrieve the Cloudflare API key I stored in Google Secret Manager before establishing the backend.